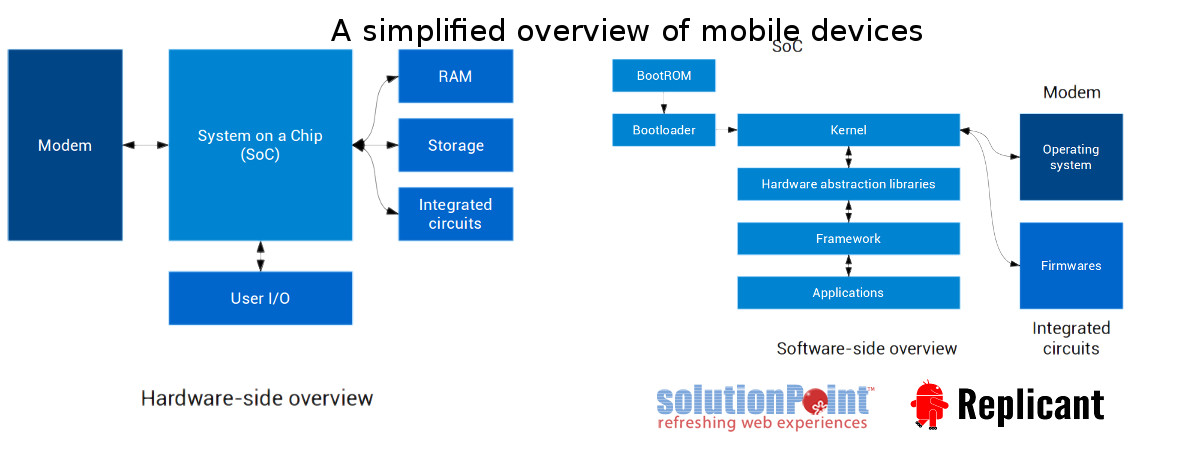
Hardware-side overview: On the hardware side, mobile devices are built with a system on a chip (SoC) that includes a processor (CPU) and other fundamental components, around which are found various integrated circuits, memory (RAM), storage, user input / output (I/O), etc. When a device is telephony-enabled, it also features a modem, which is the component dealing with the mobile telephony network. This component embeds a powerful processor that runs an operating system, along with dedicated volatile memory. Its storage can be dedicated or shared with the main processor.
Regarding the software side of things on mobile devices, the main CPU (inside the SoC) starts by executing hard-wired boot instructions (that cannot be changed), known as the bootrom. It will look up various places such as NAND, eMMC or MMC (SD / Micro SD Card) storage, depending on the hardware configuration, to load a bootloader. The bootloader, which is in fact often split in different stages, is in charge of bringing up and configuring various aspects of the hardware and eventually starting the operating system by loading and running its kernel.
Software-side overview: The kernel itself, among other things, deals with the hardware directly and provides ways for other programs (running in user-space) to access it. In user-space, hardware abstraction layers are programs specific to each device that know how to properly drive the hardware. They use the kernel to communicate back and forth with the hardware and implement the proper protocols for it.
The actual knowledge of how to drive the hardware is split between the kernel and the hardware abstraction layer libraries: both are needed to make it work properly. Hardware abstraction layers provide a generic interface for the framework to use. The framework itself provides an interface for applications that is independent of the device and the hardware. That way, applications can access hardware features through the generic framework interface, which will call the hardware abstraction layer libraries, ending up with the kernel communicating with the hardware. For instance, when placing a call, the dialer application will communicate with the framework, which in turn will communicate with the hardware abstraction layer. That hardware abstraction layer will implement the protocol to communicate with the modem. The kernel will then forward the communication between the hardware abstraction layer and the modem.
Many other components of a mobile device also run software in different forms. The various integrated circuits run small pieces of dedicated software that are called firmwares. When the device is telephony-enabled, there is also software running on the modem. Modern modems are complex and run full operating systems that are as much vulnerable to attacks and misuse like many other deliberately compromised devices close to your connected bodies made by software & hardware profiteers looking for as much bucks from few dollars worth of invention done by wiser ancestors.
Mobile telephony operators and privacy:
Even though telephony-enabled mobile devices hold a tremendous potential for spying on the user, they are not the only tools that can be used to spy in the mobile world. Most mobile telephony operators & its partners like Whatsapp keep track of every message and call made by the user, and also gather real time position of users, filter their mobile data networks and provide security agencies & paying advertisers unlimited access to that data, to an extent that depends on the operator, the country and the government. Its nothing less than live hidden cameras inside your bathroom, bedroom, and what not, we are assets of the führer with an AADHAR stamp, be nude and bow.
As these issues are fundamentally political and not technical (even though technical workarounds are possible in some cases), the proper way to solve those is to demand progress and take political action. It is especially important as the tendency for governments is to worsen the situation by allowing more and more tracking and spying on the users.
Source: Replicant, a fully free Android distribution running on several devices, a free software mobile operating system putting the emphasis on freedom and privacy / security.